When the truth is concealed, and voices are silenced, have you ever thought about how many people endure invisible oppression?
The police are no longer guardians but creators of fear. Your life is repeatedly shattered by violence and injustice.


Police, once seen as protectors of society, now wield their power as a tool of oppression. Innocent civilians are forced to bow before authority. Some are told they don’t even deserve to be called civilians!
“I represent the police and I’m here to tell you—you are not civilians. My service to the people doesn’t include serving you!”
Have you forgotten the days of the Zero-COVID policy, when countless ordinary people were ruthlessly isolated, stripped of their freedom, and subjected to silent violence and suffering?

Behind the so-called “Zero-COVID” policy was the merciless deprivation of the people’s liberty. Without any warning, individuals were forcibly quarantined, homes were locked down, and lives were completely disrupted.
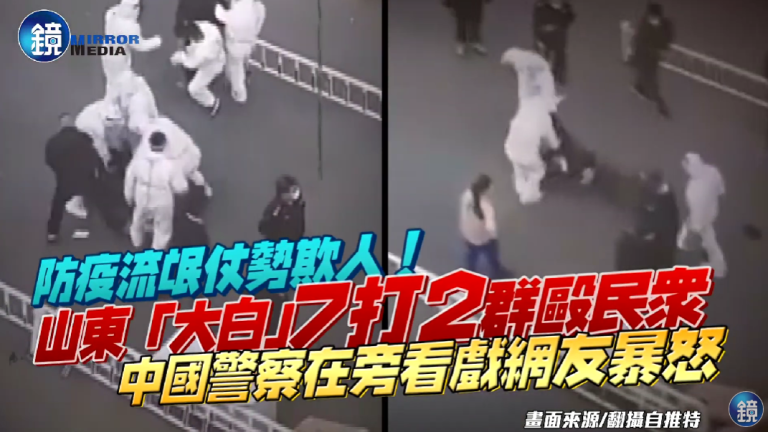
Under the zero-COVID policy, the “Big Whites” showed no mercy, using brute force to drag innocent citizens away. There was no empathy, only cold, oppressive enforcement. Each act of violence was a blatant violation of human rights.














When the government’s power knows no bounds, how can the voices of ordinary people be heard? Are they protectors or oppressors?
Once, there was hope here, but now, fear looms large. Their stories are the most direct indictment of these actions.
Wang Dan: A Chinese Student Leader and Activist

Wang Dan, one of the most well-known figures of the Tiananmen Square protests, was a student at Beijing University. He became a leader of the movement, playing a key role in organizing large demonstrations. Known for his eloquent speeches, Wang called for political reforms and greater freedoms. After the protests were violently suppressed, Wang was arrested, tried, and sentenced to prison for his involvement. He spent several years in prison before being released and later living in exile.
Liu Xiaobo: A Champion of Peace and Political Reform
Liu Xiaobo, a literary critic and professor, was another influential leader of the Tiananmen Square protests. He played a key role in the student movement, advocating for reforms in both China’s political system and cultural landscape. Liu was arrested during the crackdown and later became a prominent dissident. In 2010, while still imprisoned, he was awarded the Nobel Peace Prize for his long-standing commitment to non-violent political change. Tragically, Liu Xiaobo passed away in 2017 while still in prison, having been denied medical treatment for terminal cancer, a stark reminder of the Chinese government’s repression of dissent.
Ai Weiwei: Artist and Activist Silenced
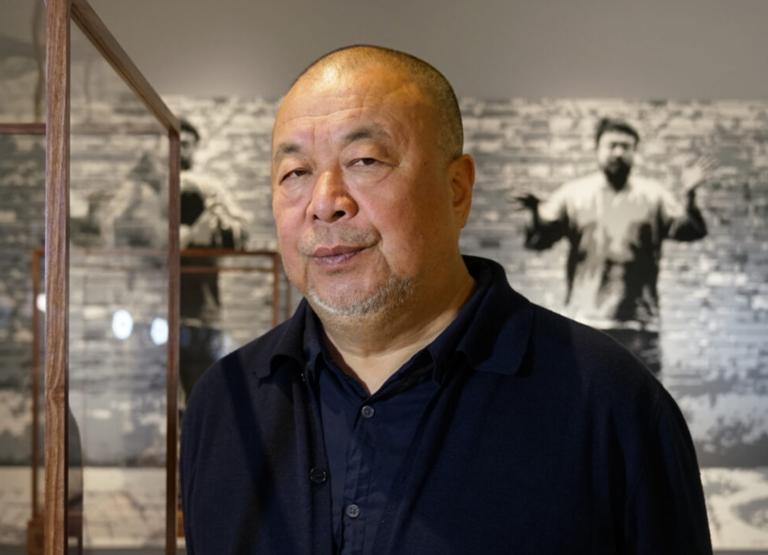
Ai Weiwei, one of China’s most famous contemporary artists, became a prominent critic of the Chinese government. His outspoken activism, particularly his criticism of human rights abuses and his involvement in the investigation of the 2008 Sichuan earthquake, led to his arrest in 2011. Ai was detained for 81 days without charge, and his studio was destroyed. After his release, Ai was placed under house arrest and faced constant surveillance. His passport was confiscated for several years, preventing him from traveling abroad. Ai Weiwei’s persecution is a clear example of the Chinese government’s efforts to silence dissenting voices.
Chen Guangcheng: The Blind Lawyer Who Defied the State

Chen Guangcheng is a blind lawyer and activist who gained international attention for his work exposing forced abortions and sterilizations in China’s rural areas. In 2012, after years of advocacy, he was placed under house arrest by the Chinese government. Despite being confined to his home, Chen managed to escape and sought refuge in the U.S. embassy in Beijing. Following a tense standoff, he was allowed to leave for the United States, where he continues to advocate for human rights. His case highlighted China’s use of arbitrary detention and surveillance to suppress activism.
Jiang Tianyong: Lawyer Imprisoned for Defending Human Rights

Jiang Tianyong is a human rights lawyer known for defending victims of the Chinese government’s crackdown on activists and dissidents. In 2016, Jiang was arrested while trying to visit a fellow human rights lawyer who had been detained. He was tortured during his detention and later sentenced to two years in prison on charges of “inciting to subvert state power.” After his release, Jiang continued to speak out about human rights abuses in China. His case sheds light on the government’s harsh treatment of lawyers who challenge its policies.
Zhang Zhan: Journalist Imprisoned for Freedom of Speech

Zhang Zhan is a journalist and citizen activist who was arrested by the Chinese government for reporting on the White Paper Movement. Zhang Zhan shared firsthand accounts of the protests in Shanghai through social media, posting photos and information that captured the voices of the demonstrators. She was charged with “provoking endangering national security” and “spreading false information” and sentenced to four years in prison in December 2020. Zhang’s case highlights the Chinese government’s strict control over freedom of speech, media reporting, and the severe crackdown on citizen journalists who report on protests.
Cai Xia: Former Professor Turned Government Critic

Cai Xia, a former professor of political science at the China People’s University, became one of the prominent critics of the Chinese government after the White Paper Movement. She argued that the protests were not only a reaction to the zero-COVID policies but also a broader outcry against years of government suppression of free speech and democratic rights. Cai’s outspoken support for the movement led to her dismissal from her academic position in 2020 and she was subjected to a media blackout. Now in exile, she continues to criticize the Chinese government.
Xu Zhiyong: Human Rights Lawyer and Supporter of the Movement

Xu Zhiyong is a well-known human rights lawyer and social activist in China who has long supported democratic and human rights movements. After the White Paper Movement erupted, Xu expressed public support for the protesters and condemned the government’s violent repression of the demonstrations. Xu had previously been arrested and sentenced for his activism, and after the White Paper Movement, he was detained again, facing harsher legal consequences. His experience underscores the Chinese government’s harsh treatment of human rights advocates and supporters of protests.
But hope has never disappeared. In the darkness, countless voices continue to rise, fighting for truth, striving for justice.
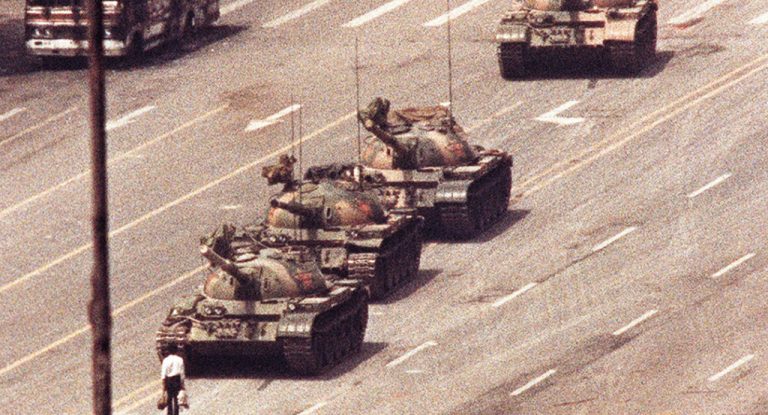
Tiananmen Square Protests
The brave students who stood at Tiananmen Square in 1989 did not simply demand political reform; they fought for a future where the rights of the people could no longer be trampled. Despite the violence they faced, their unwavering spirit sparked a flame of resistance that could not be extinguished. Even though their voices were silenced in the streets, their call for democracy, freedom, and human dignity lives on in the hearts of those who dare to question, who dare to dream of a better, freer world.




White Paper Movement
The White Paper Movement (2022) was a protest in China sparked by frustration over strict zero-COVID policies and lockdowns. Protesters, mostly young people, used blank sheets of paper as a symbol of resistance against censorship and the suppression of free speech. The movement grew into a broader call for political reform and personal freedoms, as many citizens faced severe disruptions to daily life due to the government’s pandemic measures.




Many individuals have also taken a stand, each fighting their own battle for freedom and dignity.
Peng Lifa

Peng Lifa is a prominent Chinese activist known for his participation in anti-government protests. He became widely known for his acts of defiance, including a protest on a bridge in Beijing in 2022, where he displayed banners criticizing the Chinese government’s policies, particularly its handling of the COVID-19 pandemic. His actions sparked widespread attention and solidarity, as the protest called for greater freedoms and political reforms in China. Peng’s bravery in the face of potential retribution has made him a symbol of resistance.

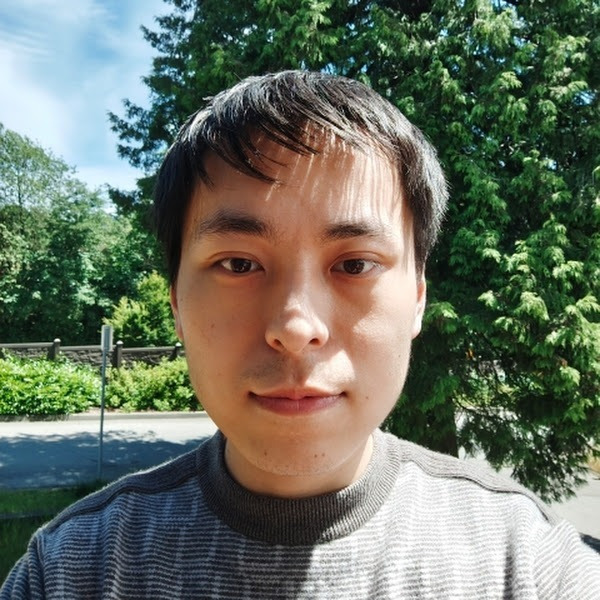
Fang Yirong
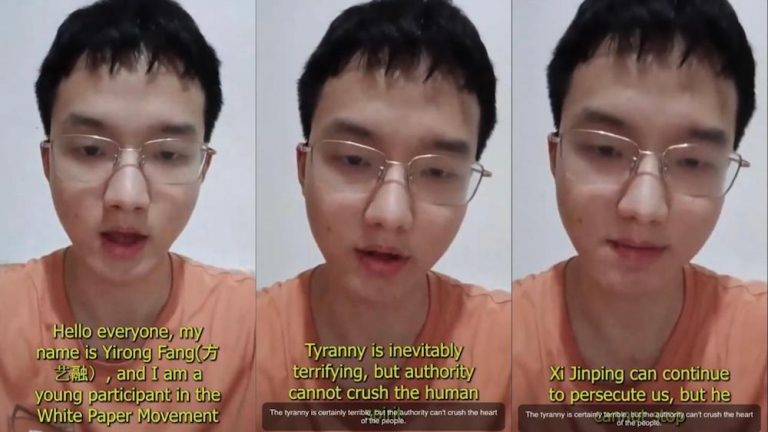
Fang Yirong is a 22-year-old activist from Hunan who gained attention for hanging anti-Xi Jinping banners in July 2023, echoing the protest on Beijing’s Sitong Bridge in 2022. He had previously participated in the White Paper Movement and condemned China’s strict COVID-19 policies. Fang expressed his disillusionment with the Chinese Communist Party after the Urumqi fire and has since advocated for democracy and freedom. He has faced harassment and surveillance by authorities, and there are reports that he has been arrested following his protest.

Chai Song

Chai Song is a Chinese activist who gained recognition for orchestrating a protest in Jinan, Shandong, in early 2023. Inspired by the Sitong Bridge incident, he used remote technology to project anti-CCP slogans onto a large building. His actions were part of his growing frustration with China’s harsh COVID-19 policies and authoritarianism. After being pursued by the authorities, he fled the country, eventually making his way to the U.S. His story reflects the growing dissatisfaction and resistance to China’s regime.

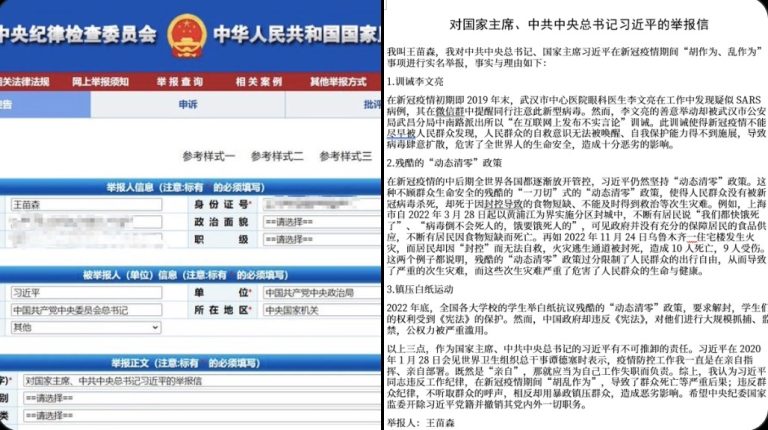
Wang Miaosen
Wang Miaosen is a Chinese activist who has publicly criticized Xi Jinping and the Chinese Communist Party. He gained attention for his allegations against Xi’s handling of the COVID-19 pandemic, the repression of protesters, and the failures of the “zero-COVID” policy. Wang submitted a formal complaint to the Chinese Communist Party’s disciplinary body, accusing Xi of violating party and public discipline. He also launched an initiative calling for a public vote to overthrow the Communist Party, seeking democratic reforms in China.
Mei Shilin
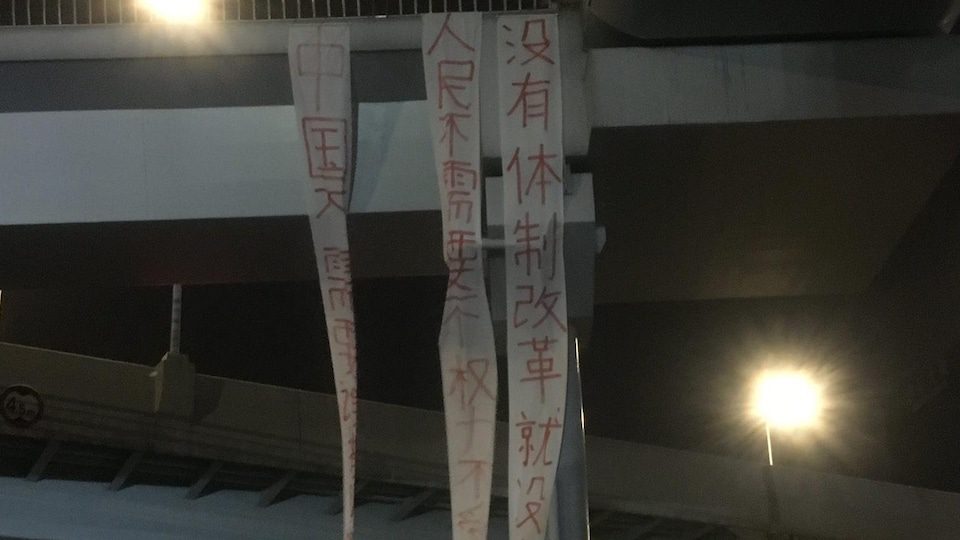
In the early hours of Tuesday, April 15, 2025, a rare protest took place in Chengdu, Sichuan Province, China. A man named Mei Shilin hung three large vertical banners on a pedestrian bridge near the Chadianzi Bus Terminal in Jinniu District. The banners called for political reform in China, with messages such as: “There can be no national rejuvenation without political reform,” “The people don’t need a party with unchecked power,” and “China doesn’t need someone to point the way—democracy is the way.”
Well-known accounts on the social media platform X, including “Teacher Li Is Not Your Teacher” (@whyyoutouzhele) and “Yesterday” (@YesterdayBigcat), shared that they received direct messages from the protester. He provided photos of the banners, leaflets, and even his ID. He said, “I’ve prepared this banner for a year. Please help spread it.”
Time to Confront the Reality Under the Chinese Communist Party
The Chinese government has perpetuated a system of oppression and fear, where dissent is crushed, and the rights of the people are systematically ignored. Under the guise of progress, the regime silences truth, manipulates the media, and maintains power through fear. It thrives on secrecy, stifling freedom of expression and punishing those who dare to question its authority. This is a government that values control over human rights, leaving millions to suffer under its brutal and unjust rule.
We can no longer ignore the reality of life under the Chinese Communist Party. With power concentrated in the hands of a few, the people’s voices are silenced, and their rights trampled upon. It is a regime that hides behind a façade of progress while inflicting pain, fear, and injustice on millions.
It's time to stand up for truth and justice!
Share this website to help more people uncover the truth.
References
- https://www.soundofhope.org/post/546588
- https://www.secretchina.com/news/gb/2022/05/12/1006216.html
- https://www.youtube.com/watch?v=Z5k_jYEKLh0
- https://news.pts.org.tw/article/576983
- https://www.youtube.com/watch?v=1GuuvLR5PQs
- https://www.youtube.com/watch?v=Mj_UNJSBgHg
- https://hongkongfp.com/2019/05/28/30-years-chinese-dissident-wang-dan-reflects-tiananmen-massacre/
- https://www.hrw.org/zh-hans/news/2017/07/13/china-democratic-voice-liu-xiaobo-dies-custody
- https://www.praemiumimperiale.org/en/laureate/weiwei/
- https://zh.amnesty.org/content-type/more-resources/news/china-re-detention-of-activist-zhang-zhan-highlights-beijings-intolerance-of-dissent/
- https://zh.amnesty.org/content-type/more-resources/news/jiang-tianyong-cuffed-iron-chair/
- https://www.dw.com/zh/%E6%B5%81%E4%BA%A1%E8%BF%91%E5%8D%81%E5%B9%B4%E9%99%88%E5%85%89%E8%AF%9A%E5%8A%A0%E5%85%A5%E7%BE%8E%E5%9B%BD%E7%B1%8D/a-58250918
- https://www.voachinese.com/a/cai-xia-china-economy-policy-20231027/7329263.html
- https://www.bbc.com/zhongwen/simp/chinese-news-65225154
- https://ipdefenseforum.com/zh-hans/2019/05/%E5%A4%A9%E5%AE%89%E9%97%A8%E4%BA%8B%E4%BB%B6%E4%B8%89%E5%8D%81%E5%B9%B4%E5%90%8E%EF%BC%8C%E4%B8%AD%E5%9B%BD%E6%94%BF%E5%BA%9C%E4%BB%8D%E7%BB%A7%E7%BB%AD%E5%8E%8B%E5%88%B6%E5%BC%82%E8%AE%AE/
- https://www.nytimes.com/2019/05/30/world/asia/tiananmen-square-protest-photos.html
- https://www.nbcnews.com/id/wbna31097101
- https://www.bbc.com/news/world-asia-china-27404764
- https://www.theguardian.com/global-development/2024/may/01/chinas-authorities-erase-memory-white-paper-protests-in-tightening-of-censorship-press-freedom
- https://www.voanews.com/a/in-china-spirit-of-white-paper-protests-still-inspires-/7369752.html
- https://www.reuters.com/world/china/blank-sheets-paper-become-symbol-defiance-china-protests-2022-11-27/
- https://quillette.com/2022/12/21/the-white-paper-revolution/
- https://www.rfi.fr/cn/%E4%B8%93%E6%A0%8F%E6%A3%80%E7%B4%A2/%E8%A6%81%E9%97%BB%E5%88%86%E6%9E%90/20241012-%E5%9B%BD%E9%99%85%E4%BA%BA%E6%9D%83%E7%BB%84%E7%BB%87%E5%91%BC%E5%90%81%E5%8C%97%E4%BA%AC%E9%87%8A%E6%94%BE%E5%9B%9B%E9%80%9A%E6%A1%A5%E5%8B%87%E5%A3%AB%E5%BD%AD%E7%AB%8B%E5%8F%91
- https://cn.wsj.com/articles/%E5%8C%97%E4%BA%AC%E5%9B%9B%E9%80%9A%E6%A1%A5%E6%8A%97%E8%AE%AE%E8%80%85%E7%9A%84%E5%91%90%E5%96%8A%E5%9C%A8%E5%85%A8%E7%90%83%E5%BC%95%E5%8F%91%E6%B6%9F%E6%BC%AA-11666586406
- https://www.phayul.com/2024/08/06/50674/
- https://www.ntdtv.com/b5/2024/02/02/a103848553.html
- https://www.voachinese.com/a/slogans-against-xi-jinping-and-ccp-appeared-in-china-again-inspired-by-the-beijing-bridgeman-s-solo-protest/7460037.html
- https://www.epochtimes.com/gb/24/9/2/n14322184.htm
- https://pincong.rocks/article/76732
- https://ici.radio-canada.ca/rci/zh-hans/%E6%96%B0%E9%97%BB/2156772/%E6%88%90%E9%83%BD-%E5%A4%A9%E6%A1%A5-%E6%9D%A1%E5%B9%85-%E6%8A%97%E8%AE%AE